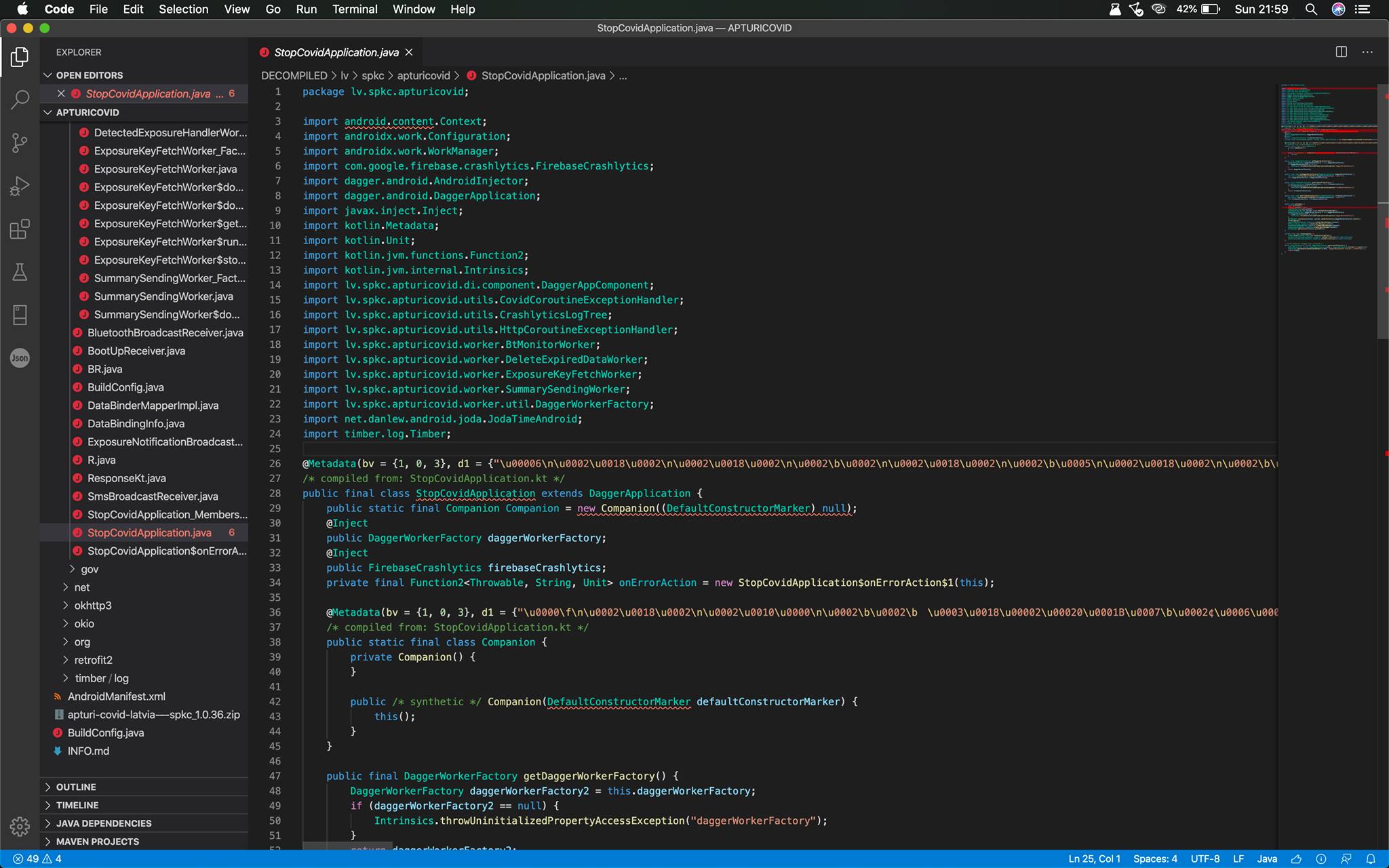
Due to many subjective opinions around the internet whether or not the application is safe-to-use, I decided to decompile it and check as-is. I am in no way affiliated with SPKC and a completely independent person from the project. At the end of the post I've attached downloadable source code for further researching.
Permissions
- android.permission.ACCESS_NETWORK_STATE view network status Allows an application to view the status of all networks.
- android.permission.BLUETOOTH create Bluetooth connections Allows an application to view configuration of the local Bluetooth phone and to make and accept connections with paired devices.
- android.permission.FOREGROUND_SERVICE Allows a regular application to use Service.startForeground
- android.permission.INTERNET full Internet access Allows an application to create network sockets.
- android.permission.RECEIVE_BOOT_COMPLETED automatically start at boot Allows an application to start itself as soon as the system has finished booting. This can make it take longer to start the phone and allow the application to slow down the overall phone by always running.
- android.permission.WAKE_LOCK prevent phone from sleeping Allows an application to prevent the phone from going to sleep.
- com.google.android.c2dm.permission.RECEIVE C2DM permissions Permission for cloud to device messaging.
- com.google.android.finsky.permission.BIND_GET_INSTALL_REFERRER_SERVICE Unknown permission from android reference Unknown permission from android reference
So what we can already understand from here, your contacts are staying untouched as the application can’t even read your contacts without permission “android.permission.READ_CONTACTS”.
Endpoints
lv/spkc/apturicovid/BuildConfig.java
- https://apturicovid-api.spkc.gov.lv/api/
- https://apturicovid-files.spkc.gov.lv/exposure_configurations/v1/android.json
- https://apturicovid-files.spkc.gov.lv/dkfs/v1/index.txt
- https://apturicovid-files.spkc.gov.lv/stats/v1/covid-stats.json
lv/spkc/apturicovid/worker/ExposureKeyFetchWorker$storeExposureCheckTokens$2.java
- https://apturicovid-files.spkc.gov.lv/dkfs/v1/index.txt
Firebase
- https://apturicovid.firebaseio.com
Network
- @POST(“v1/phone_verifications“) Object createPhoneVerification(@Body PhoneVerificationCreateBody phoneVerificationCreateBody, Continuation<? super TokenResponse> continuation);
- @POST(“v1/diagnosis_keys“) Object sendDiagnosisKeys(@Body Diagnosis diagnosis, Continuation<? super Response<Object>> continuation);
- @POST(“v1/exposure_summaries“) Object sendExposureSummaries(@Body ExposureSummary exposureSummary, Continuation<? super Unit> continuation);
- @POST(“v1/phone_verifications/verify“) Object verifyPhone(@Body PhoneVerificationBody phoneVerificationBody, Continuation<? super PhoneVerificationResponse> continuation);
- @POST(“v1/upload_keys/verify“) Object verifyUploadKeys(@Body UploadPinVerificationBody uploadPinVerificationBody, Continuation<? super TokenResponse> continuation);
This is the only data that is being sent to the endpoint server. Seems pretty reasonable for me.
Conclusion
I was unable to find anything harmful within the application, that would harness your data or do anything other than the purpose of the application. For this very reason I’m attaching the decompiled Source code below, so for those who have the conspiracy theories — please make them with argumentative pointing in the Source “Look, in that file, line X, they’re sending out sensitive data” or… just don’t make conspiracy theories without any ground. So, if you want to use the application, great — it seems safe, if not — that’s fine, but don’t deceive others.
Source
De-compiled files for further analysis can be downloaded @ https://up.nils.digital/KPanBkEH/. Version is 1.0.36, May 27, 2020.Feel free to check the source code, or ask any questions. I hope this research was enough to provide current rumors wrong.
N. Putnins, Security Analyst @ Digital Security Alliance (https://www.seq.science/)

Comments are closed.